The Real Difference Between Cyber Security & Information Security
In this advanced period, each association puts its information and documents on physical or virtual servers. The innovation has facilitated the capacity and the board of data, and yet, it has likewise brought information security issues. Information and data security have turned into a critical worry for a wide range of undertakings. To shield their information base from burglary and programmers, they need to look for the assistance of oversaw IT security specialist organizations. By and large, MSP offers three kinds of safety administrations to organizations: network security, online protection, and data security. The vast majority regularly get confounded among network safety and data security. They believe that the two administrations are something very similar. However, indeed, every one of them connotes various sorts of insurance. Organizations need to comprehend the genuine contrast between these two terms to send vigorous information security. Allow us to examine the genuine contrast between the two terms.
Table of Contents
Data Security
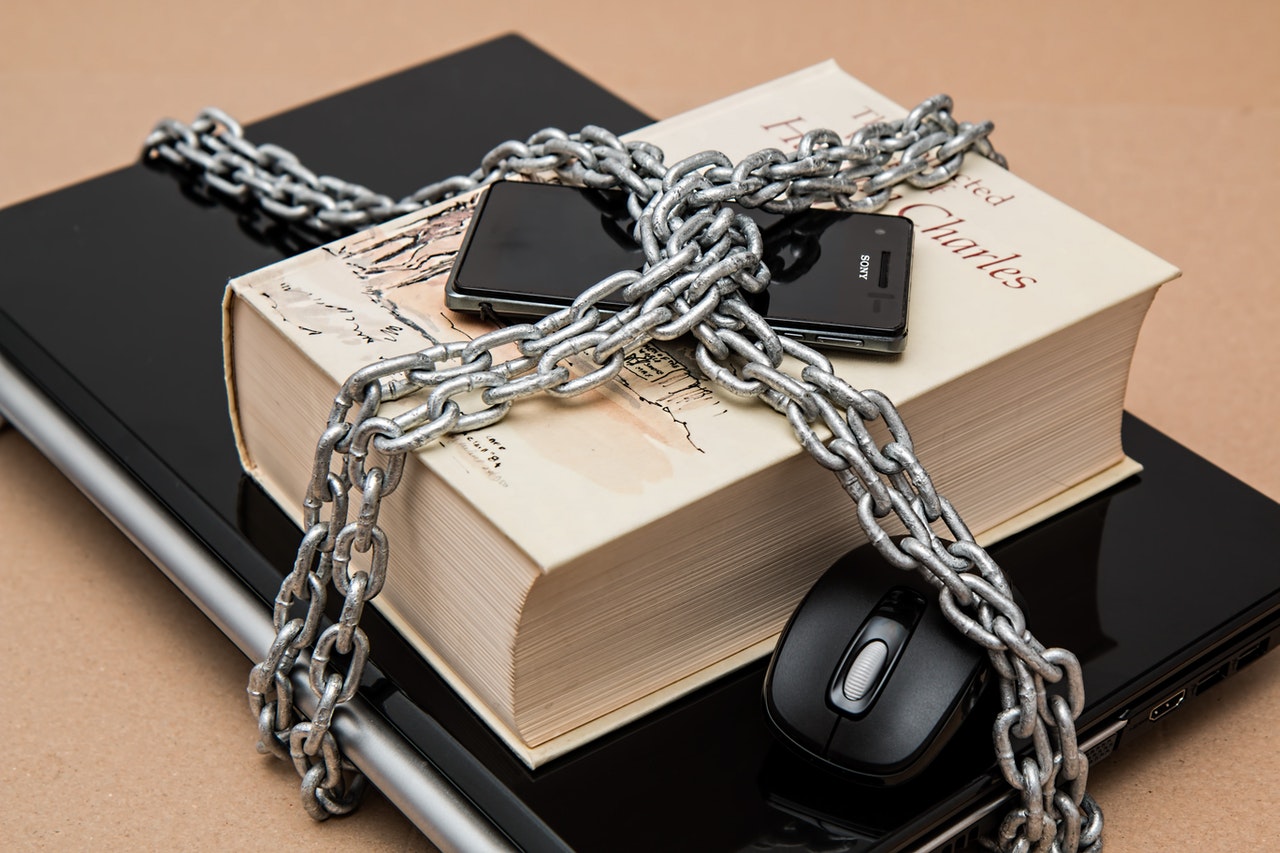
Data security is a sort of information security that means to shield the association’s classified information from any sort of unapproved access-The information can be in physical or computerized structure. The occupation of a data security proficient is to defend the secrecy, accessibility, and uprightness of an association’s data. They keep their eyes on the information when it is sent starting with one gadget then onto the next gadget or starting with one area then onto the next. Prior to continuing on, let us get knowledge into the components of data security – :
Privacy
Privacy is the primary thing that strikes a chord when you ponder information security. The data security engineers guarantee that main approved clients access the organization’s virtual and actual servers and printed information. They block ill-conceived clients and the individuals who dishonestly attempt to get to the information. Different wellbeing measures and strategies are utilized to protect information secrecy. Some of them are encryption, passwords, cryptography, biometric validation, and so on
Trustworthiness
Information trustworthiness is essential to keep up with its fulfillment, precision, and unwavering quality. The data security expert keeps information from being changed all through its lifecycle. They keep the consistency of information with the assistance of numerous product instruments.
Accessibility
Information accessibility is a crucial component of data security. It guarantees that the information and data accessible just to genuine clients. The specialists additionally hold back up touchy information in unmistakable and theoretical gadgets as a component of the debacle recuperation plan.
Network protection
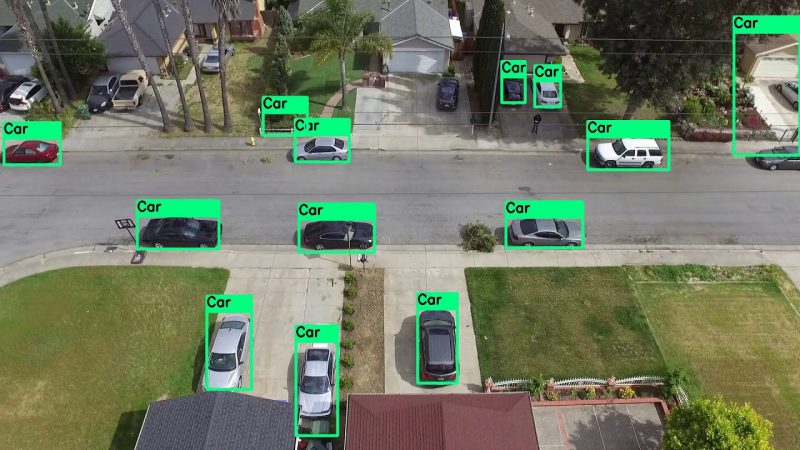
Online protection is one more kind of oversaw IT security administration used to forestall network gadgets, frameworks, and endpoints from cybercriminals and ill-conceived programmers. The job of online protection engineers is to defend an association’s organization and framework from advanced assaults. Digital assaults are performed to take private data or to obliterate the organization of the association. Some cybercriminals utilize malwares to blackmail cash from the association. This sort of safety manages just electronic information, though data security is intended to ensure both computerized and printed documents.
Kinds Of Threat From Which Cybersecurity experts secure your information
Cybercrime
Individuals make cybercrimes to bring in some cash. They generally target PCs to hack credit/check card numbers and passwords.
Digital Attack
The digital assaults are made to harm the organization and PCs in lieu of acquiring monetary benefits. Contenders typically dispatch them to keep steady over the market.
Cyberterrorism
It is a criminal demonstration that is performed to make alarm among the clients. Cyberterrorism plans to debilitate the frameworks by utilizing the accompanying malwares – :
Infection
Deception
Adware
Ransomware
Spyware
Malware is only malignant programming that disaster areas PCs or organizations. These malignant projects delayed down the speed of PCs and at last influence the efficiency of the association. The network safety expert shields your frameworks from malware by keeping framework and application virtual products modern.
The Bottom Line – :
Network safety and data security are the essential components of oversaw IT security administrations. Both intend to defend your information from unapproved access. The main distinction is that network safety manages the insurance of both electronic and paper reports, though online protection safeguards gadgets records.